Opentext
Encase Forensic
The gold standard of computer forensic tools since early stages of digital forensic era

EnCase® Forensic merupakan pemenang penghargaan Best Computer Forensic Hardware pada Forensic 4cast Awards yang diadakan oleh SANS Forensic Summit, di Austin Texas.
Investigator digital memerlukan sebuah solusi yang dapat dengan mudah menangkap data yang relevan untuk mendukung sebuah investigasi atau kebutuhan kepatutan dan memiliki kemampuan analisis teknis yang canggih untuk menemukan data yang tersembunyi. EnCase® Forensic adalah sebuah platform investigasi handal yang mengumpulkan data digital, melakukan analisis, melaporkan temuan dan menyimpannya dalam bentuk yang sesuai secara forensik digital dan dapat diterima di pengadilan.
Encase Forensic dikenal secara global sebagai Gold Standard untuk forensik digital dan satu-satunya solusi yang telah teruji di pengadilan dan dibangun dengan investigasi digital forensik yang dalam, prosesing yang kuat, dan alur kerja terintegrasi dengan opsi reporting yang fleksibel. Encase Forensic dibangun dengan pemahaman yang dalam terhadap siklus investigasi digital dan pentingnya mempertahankan integritas barang bukti. Dengan user interface yang baru dan alur kerja yang efisien, Encase Forensic memperkuat setiap examiner untuk menyelesaikan investigasi tanpa masalah.
Peningkatan Mesin Indexing
Dengan Indexing baru yang terdapat pada Encase, investigator akan memiliki kecepatan prosesing yang kuat dalam investigasinya, index searching yang lebih canggih, dukungan bahasa yang lebih baik, dan optimisasi performa.
Dengan Indexing baru yang terdapat pada Encase, investigator akan memiliki kecepatan prosesing yang kuat dalam investigasinya, index searching yang lebih canggih, dukungan bahasa yang lebih baik, dan optimisasi performa.
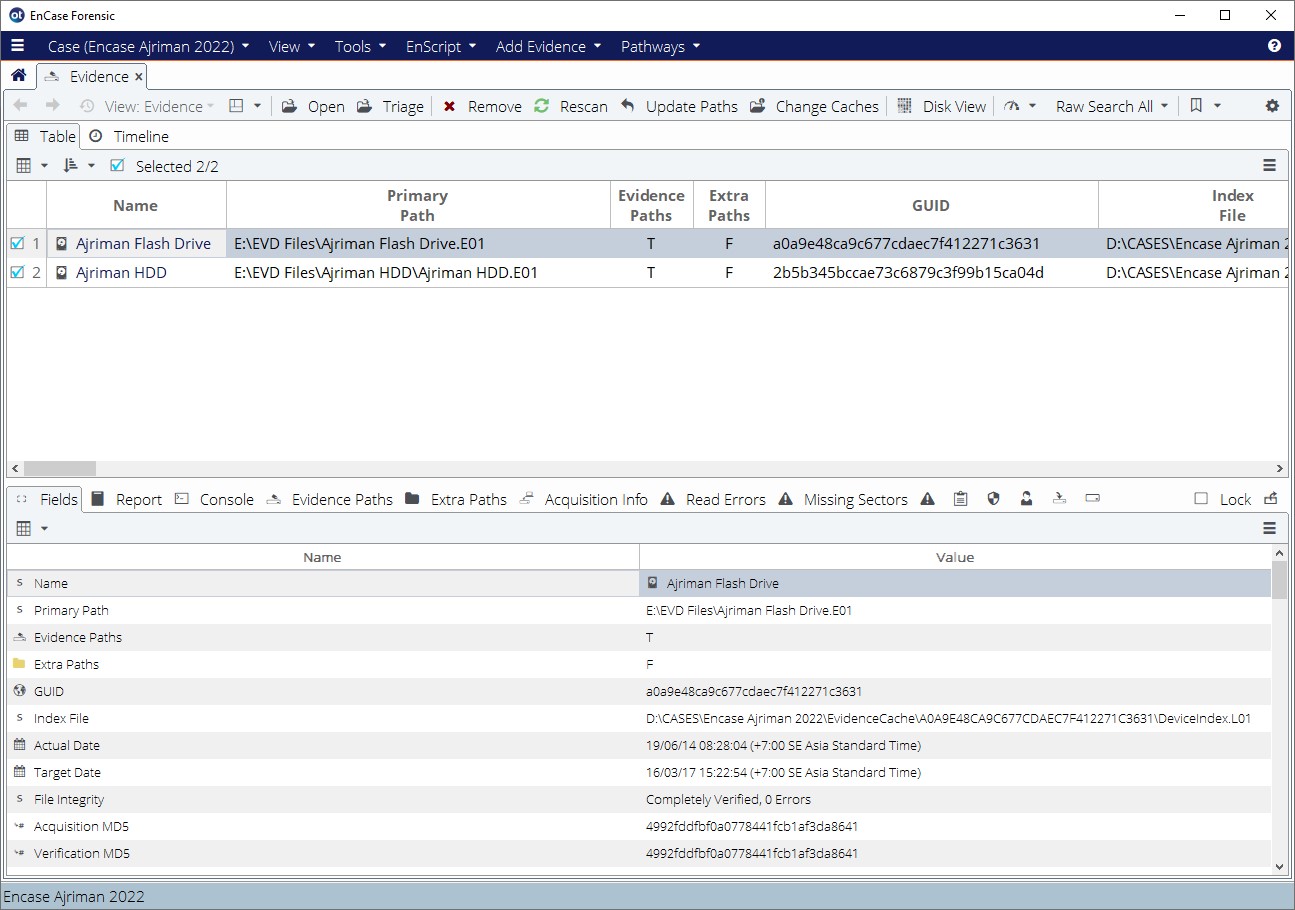
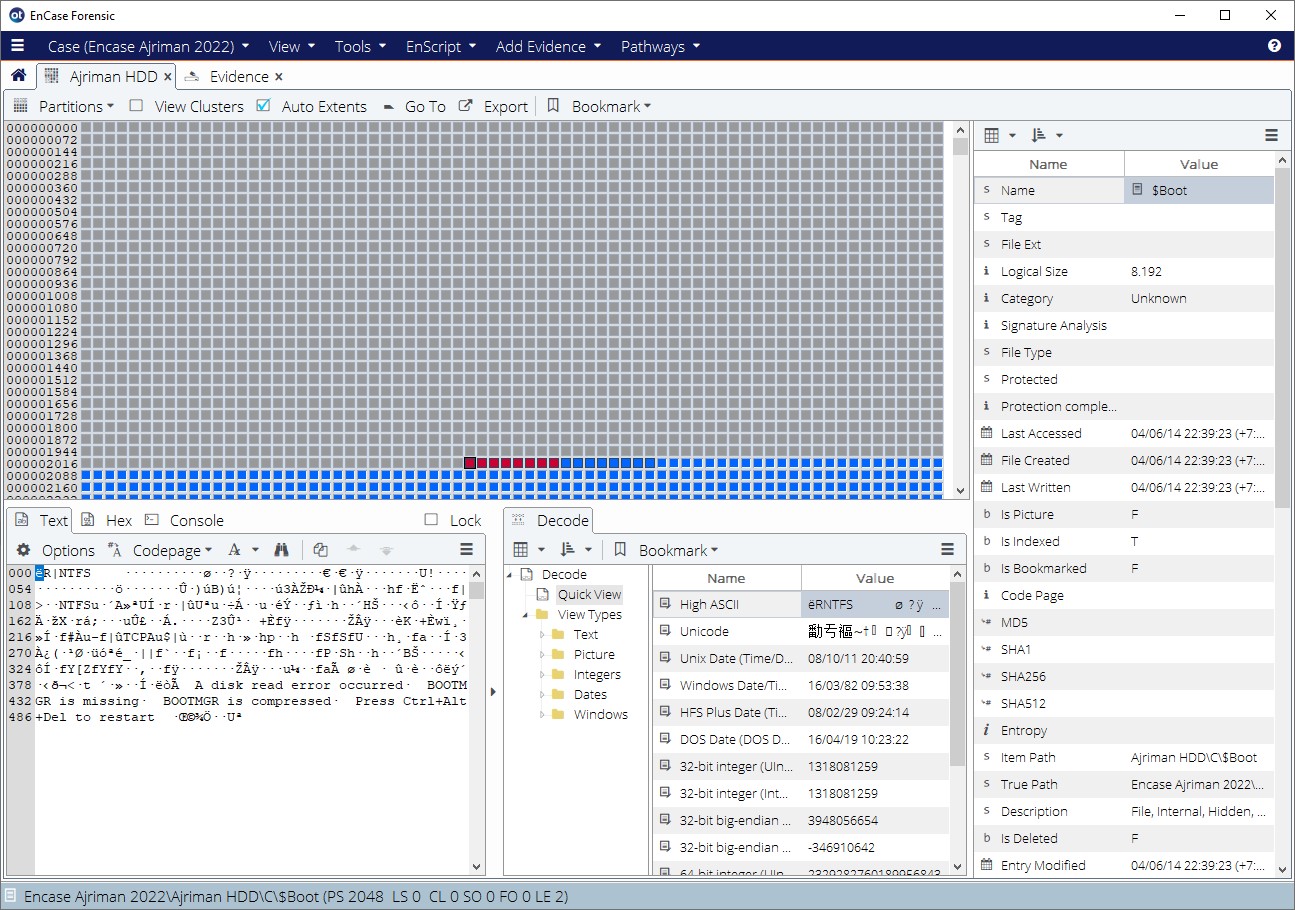
Akuisisi Barang Bukti yang Dapat Diandalkan
Dengan Encase Forensic, examiner akan yakin bahwa integritas dari barang bukti tidak akan dipermasalahkan. Semua barang bukti yang diambil dengan Encase Forensic akan disimpan dalam format evidence file yang diterima di pengadilan.
Dengan Encase Forensic, examiner akan yakin bahwa integritas dari barang bukti tidak akan dipermasalahkan. Semua barang bukti yang diambil dengan Encase Forensic akan disimpan dalam format evidence file yang diterima di pengadilan.
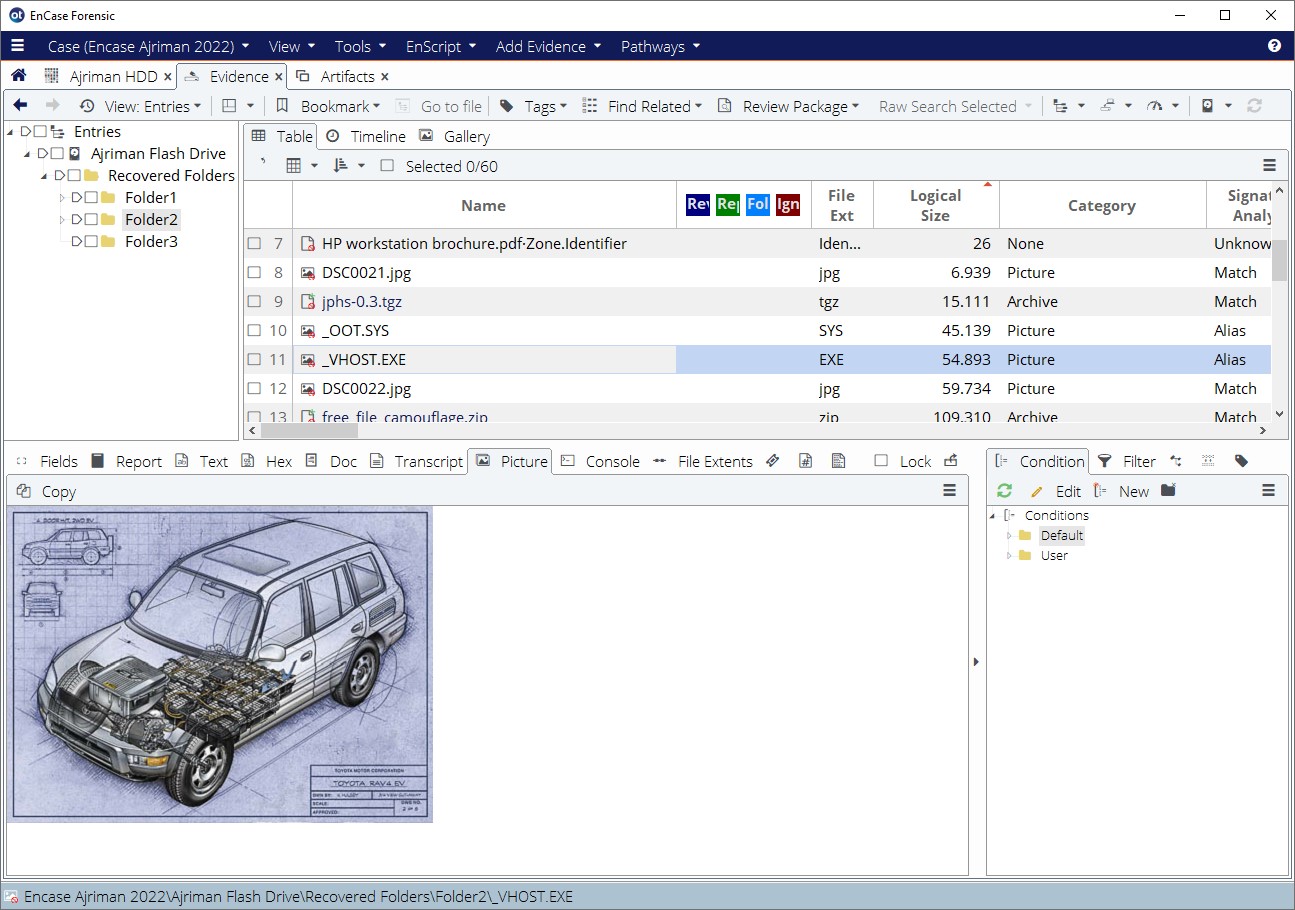
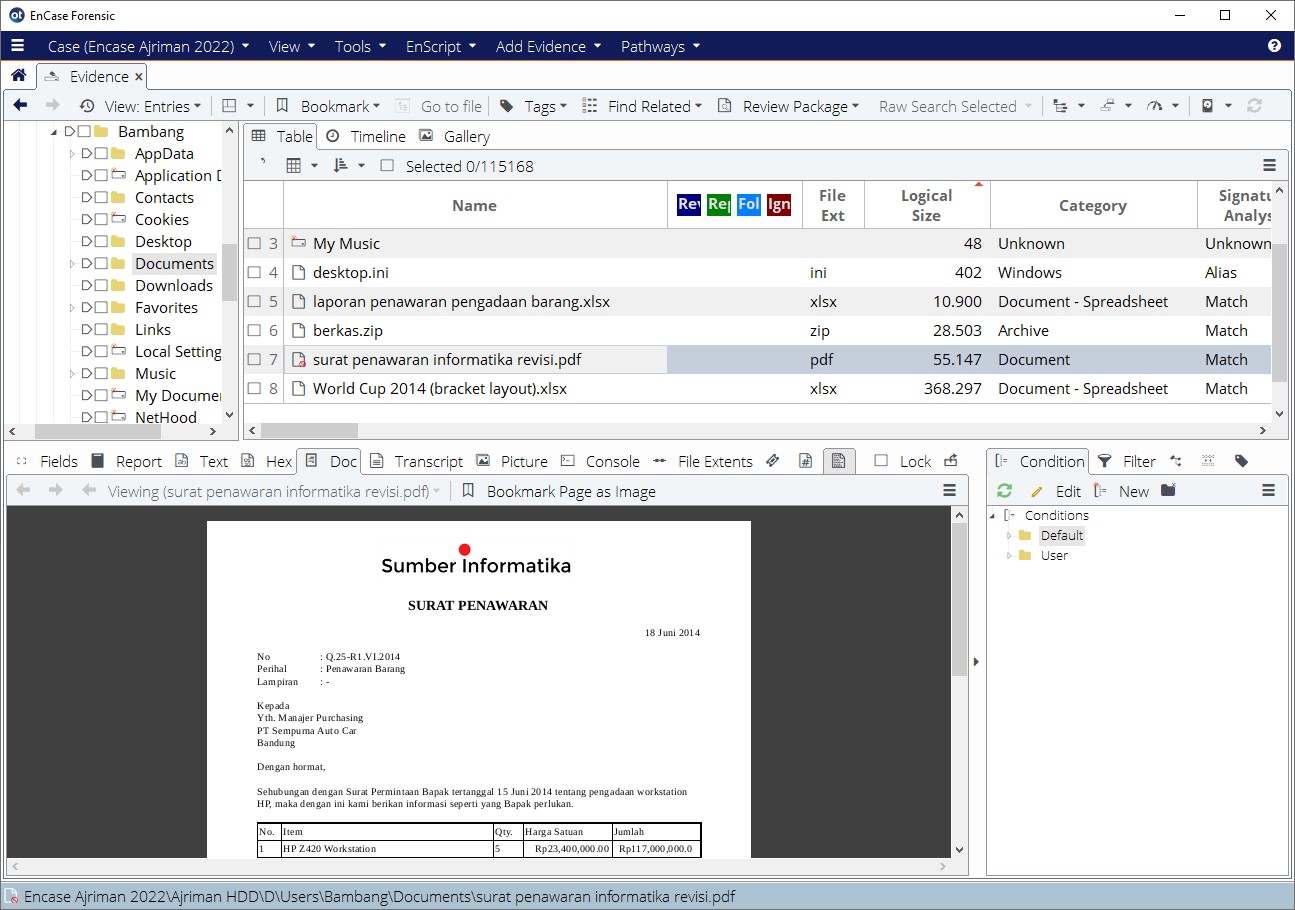
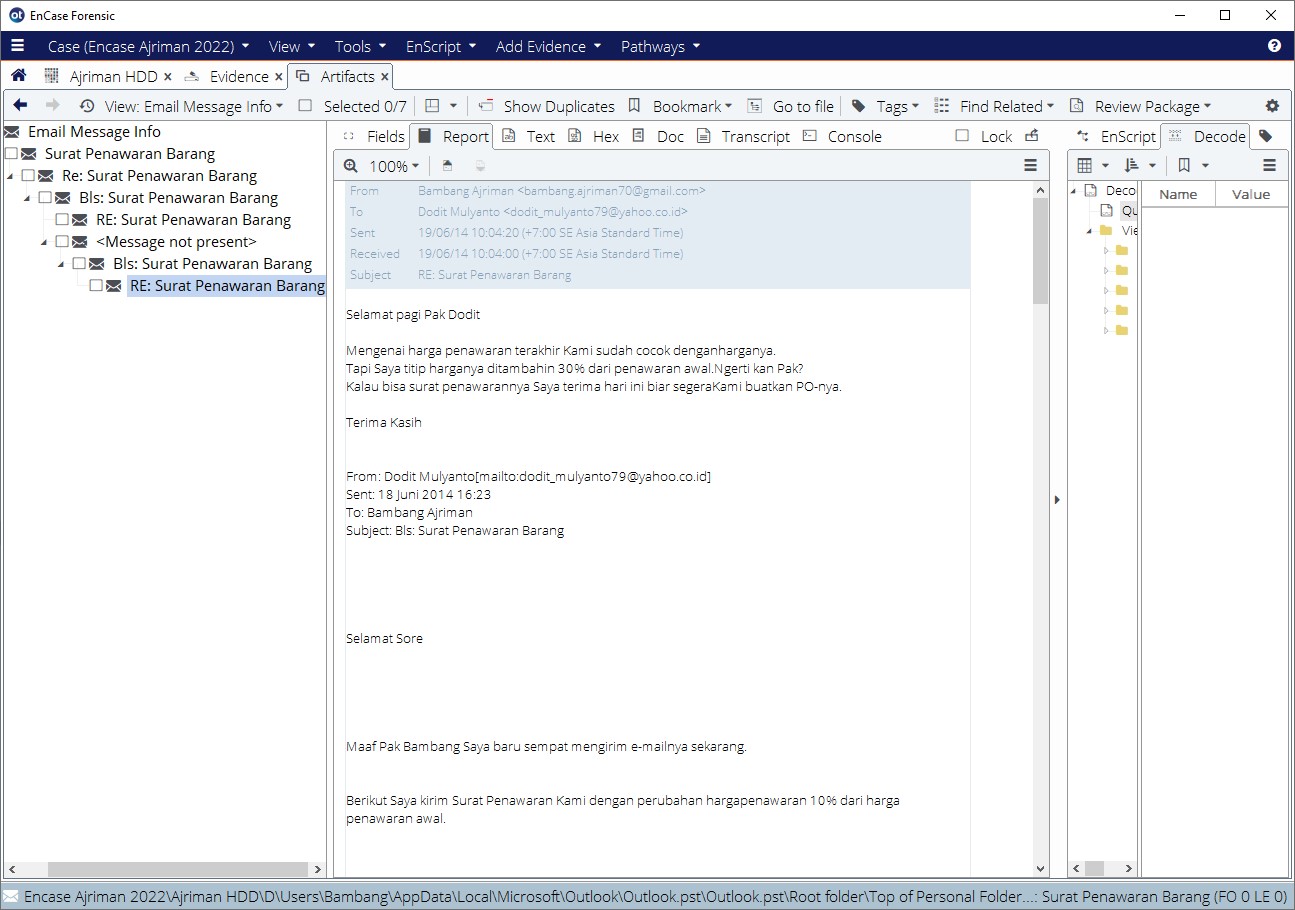
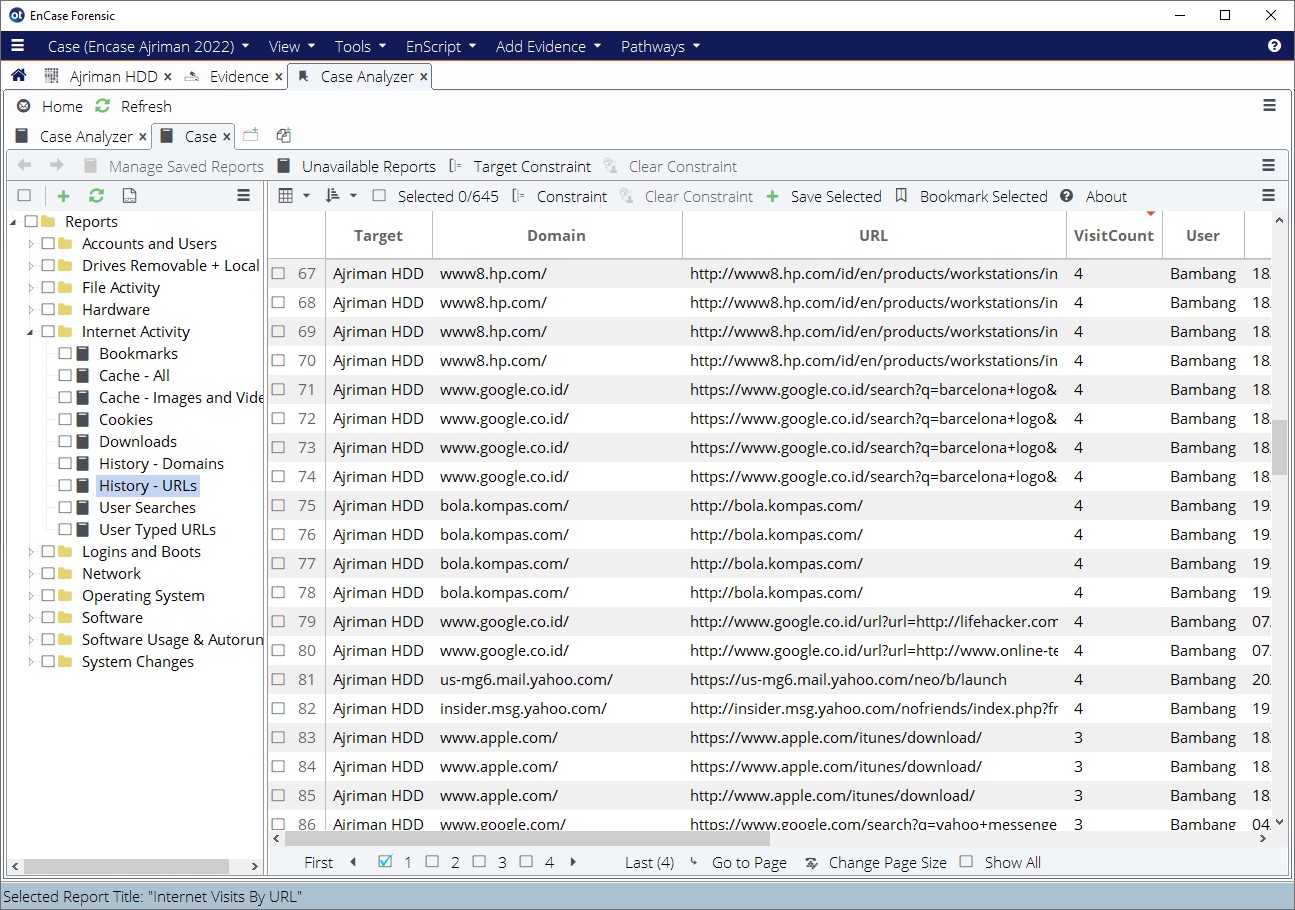
Analisis Forensik Digital yang Dalam
Encase Forensic dikenal denngan kemampuannya untuk mengungkap bukti yang dapat tidak terlihat oleh produk lain. Sebagai Gold Standard dalam digital forensik, Encase sudah digunakan pada lebih dari 100 kasus pengadilan.
Encase Forensic dikenal denngan kemampuannya untuk mengungkap bukti yang dapat tidak terlihat oleh produk lain. Sebagai Gold Standard dalam digital forensik, Encase sudah digunakan pada lebih dari 100 kasus pengadilan.
Investigasi Mobile
Dengan lisensi tambahan, anda dapat menggunakan Encase Forensic untuk smartphone dan tablet terbaru lebih dari 27,000 device yang sudah ditunjang, membantu examiner untuk melakukan akusisi logikal dan fisikal. Dari investigator awam sampai examiner berpengalaman, tiap user dapat mencari bukti yang mereka butuhkan dengan akuisisi mobile pada Encase Forensic.
Dengan lisensi tambahan, anda dapat menggunakan Encase Forensic untuk smartphone dan tablet terbaru lebih dari 27,000 device yang sudah ditunjang, membantu examiner untuk melakukan akusisi logikal dan fisikal. Dari investigator awam sampai examiner berpengalaman, tiap user dapat mencari bukti yang mereka butuhkan dengan akuisisi mobile pada Encase Forensic.
Dukungan OS/Dekripsi yang Luas
Menyediakan dukungan terluas untuk filesystem dan sistem operasi, Encase Forensic membantu investigator untuk menyediakan hasil analisis detail yang meyakinkan dari temuan.
Menyediakan dukungan terluas untuk filesystem dan sistem operasi, Encase Forensic membantu investigator untuk menyediakan hasil analisis detail yang meyakinkan dari temuan.
Reporting yang Mudah
Case yang komplit ditandai dengan adanya laporan akhir. Dengan menggukan template yang dapat dikostumisasi dari Encase Forensic, examiner dapat membuat laporan yang menyeluruh, mudah dibaca, profesional, dan dapat dibagikan untuk setiap kasus.
Case yang komplit ditandai dengan adanya laporan akhir. Dengan menggukan template yang dapat dikostumisasi dari Encase Forensic, examiner dapat membuat laporan yang menyeluruh, mudah dibaca, profesional, dan dapat dibagikan untuk setiap kasus.
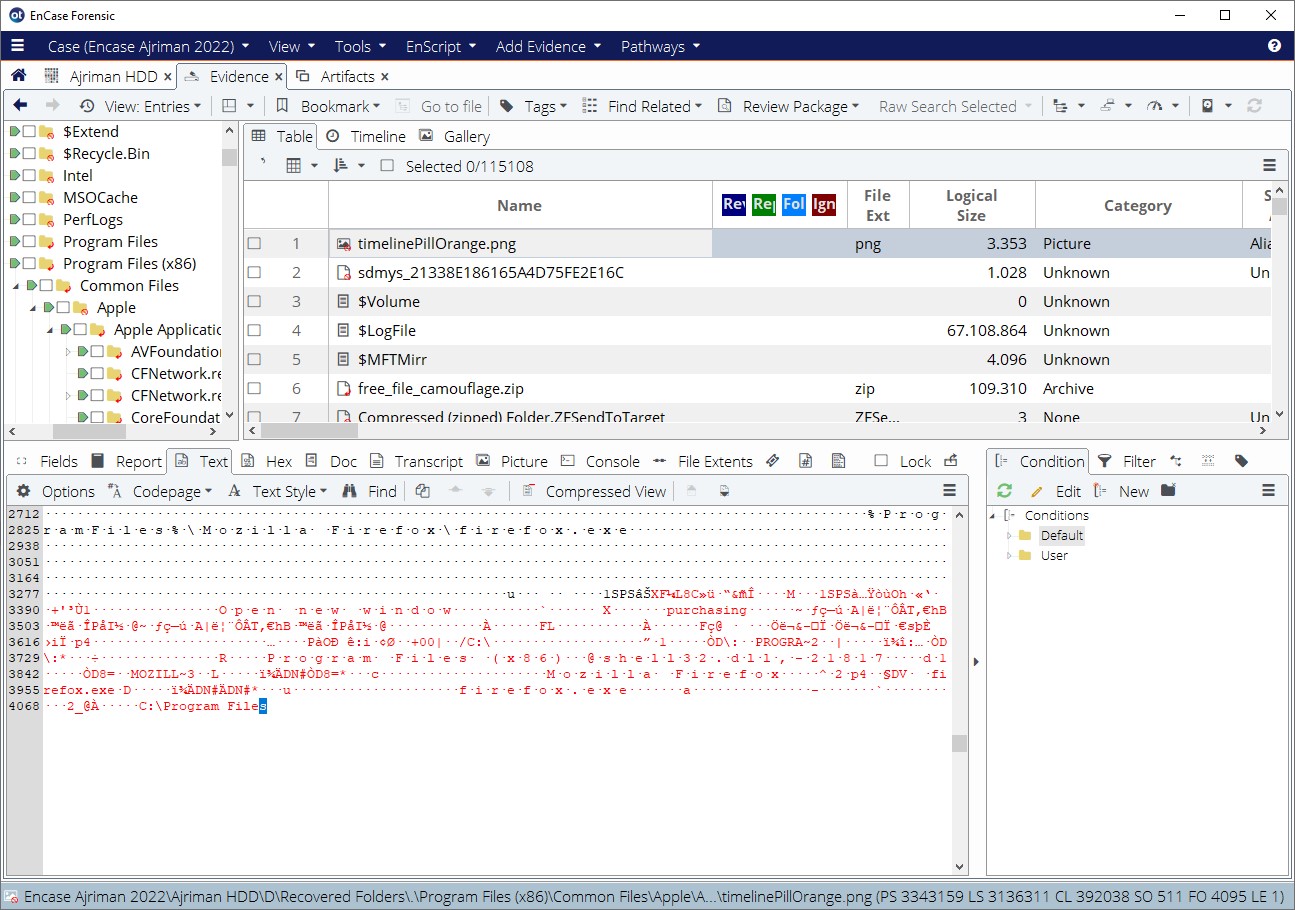
Ekstensibilitas
Encase Forensic menawarkan ekstensibilitas melalui Enscripts. Enscripts adalah kode perintah otomatis yang menjalankan tugas dan dapat dibuat oleh developer melalui AppCentral. Enscripts dapat sangat membantu memperluas kemampuan Encase Forensic untuk membantu examiner menyelesaikan investigasi dengan lebih efisien.
Encase Forensic menawarkan ekstensibilitas melalui Enscripts. Enscripts adalah kode perintah otomatis yang menjalankan tugas dan dapat dibuat oleh developer melalui AppCentral. Enscripts dapat sangat membantu memperluas kemampuan Encase Forensic untuk membantu examiner menyelesaikan investigasi dengan lebih efisien.
Otomatisasi Alur Kerja
Menghemat waktu adalah hal penting dalam investigasi. Dengan alur kerja investigasi dan filtering, examiner dapat dengan mudah mengoperasikan Encase Forensic untuk meningkatkan metode mereka dalam mengungkap bukti.
Menghemat waktu adalah hal penting dalam investigasi. Dengan alur kerja investigasi dan filtering, examiner dapat dengan mudah mengoperasikan Encase Forensic untuk meningkatkan metode mereka dalam mengungkap bukti.
Fitur Terbaru
Membangun peningkatan performa yang dikenalkan pada 8.06, versi terbaru 8.07 mengeluarkan peningkatan yang mendukung kostumer untuk lebih jauh merasakan perbedaan Encase Forensic dari tools lain yang ada. Dukungan enkripsi yang telah diperbaharui, dukungan Apple filesystem, dan kemampuan volume shadow adalah sedikit dari berbagai peningkatan baru yang dirancang untuk investigator dalam mengumpulan bukti yang mereka butuhkan secara efisien, tepat, dan dengan pengalaman user terbaik yang ada.
Membangun peningkatan performa yang dikenalkan pada 8.06, versi terbaru 8.07 mengeluarkan peningkatan yang mendukung kostumer untuk lebih jauh merasakan perbedaan Encase Forensic dari tools lain yang ada. Dukungan enkripsi yang telah diperbaharui, dukungan Apple filesystem, dan kemampuan volume shadow adalah sedikit dari berbagai peningkatan baru yang dirancang untuk investigator dalam mengumpulan bukti yang mereka butuhkan secara efisien, tepat, dan dengan pengalaman user terbaik yang ada.
Encase Forensic v20
Evolusi selajutnya dalam investigasi forensik digital
Evolusi selajutnya dalam investigasi forensik digital
Tertarik dengan produk ini?
Fitur-fitur Encase Forensic:
Klik pada gambar untuk memperbesar